
FCC reverses course, allows software updates for foreign-made drones and routers...
The FCC is extending a software lifeline for millions of already-deployed drones and routers. In late 2025 and early...
Topic
Every story in this section follows the same verification structure, attribution rules, and ad-eligibility logic.
Featured offer
Patrick Tech Store Open the AI plans, tools, and software currently getting the push Jump straight into the store to see what Patrick Tech is pushing right now.
The FCC is extending a software lifeline for millions of already-deployed drones and routers. In late 2025 and early...

There is no app that lets you pull up someone else’s call history. There never has been, and there almost certainly...

When you purchase through links on our site, we may earn an affiliate commission. Only a few days before that, the UK...

Agentic AI is already becoming a common part of how enterprises operate. But getting real value from AI depends on how...

Canvas is at the center of an ongoing cyberattack and data extortion attempt by a well-known cybercriminal group that...

Security researcher Hyunwoo Kim disclosed finding a nine-year-old flaw, and published a proof-of-concept (PoC)...

Peter Williams , a veteran cybersecurity executive who was the head of the hacking and surveillance tech division of...

The Trump administration on Friday launched a new website that will house a collection of “new, never-before-seen...
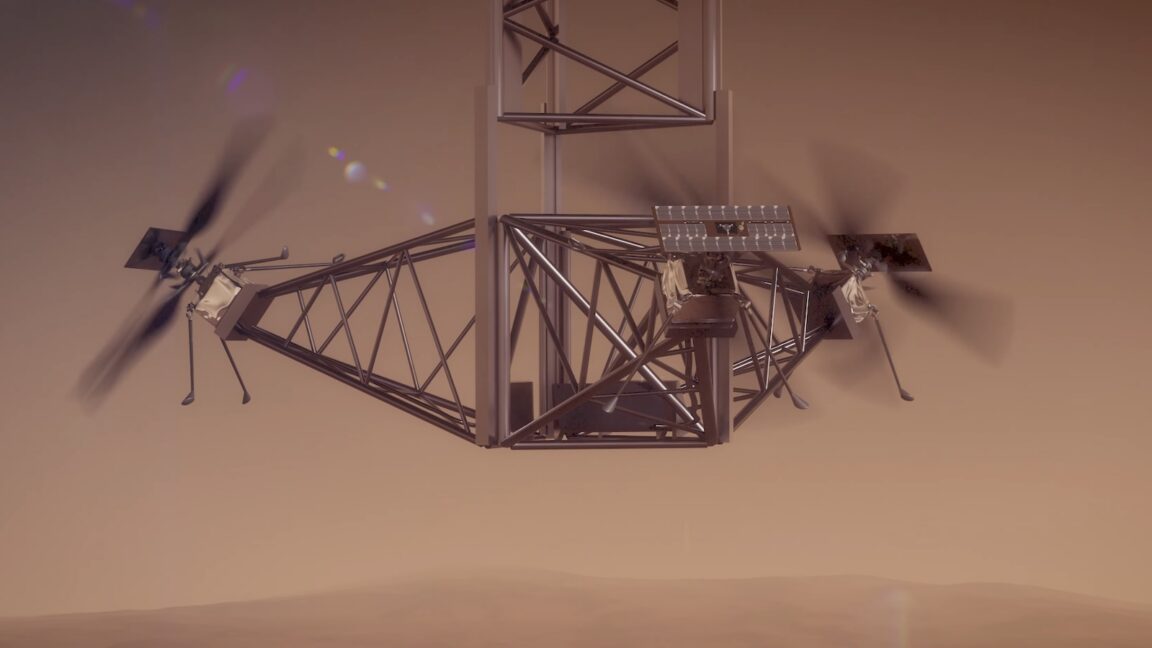
A little more than three years since NASA's Ingenuity helicopter ended its pioneering mission at Mars, engineers at...

One of the advantages of using macOS is that it offers a more secure platform than Windows. Part of the reason is that...

The dark secret of enterprise security operations is that defenders have quietly institutionalized the practice of not...

plunged more than 16% in late trading today after the content delivery network and security company beat fiscal 2026...
Many browsers, including Microsoft Edge, have built-in password management features, but they are not as secure as a...

The rise of the AI factory is reshaping how organizations build and scale intelligence — and it’s putting AI...

AI factory security begins at the hardware layer — a fact that is taking on new urgency as enterprises scramble to...

Written by Taylor Clemons, Staff Writer Staff Writer May 7, 2026 at 10:31 a.m. PT Adam Breeden/ZDNET TCL QM8 85-inch...

Enterprise AI deployment has fundamentally expanded the cybersecurity attack surface, turning data pipelines, model...

Palo Alto Networks has disclosed that threat actors may have attempted to unsuccessfully exploit a recently disclosed...

On April 29, 2026, a Linux kernel local privilege escalation vulnerability was publicly disclosed under the name "Copy...

Having an incident response retainer, or even a pre-approved external incident response firm, is not the same as being...

Cybersecurity researchers have discovered three packages on the Python Package Index (PyPI) repository that are...

A dozen critical security vulnerabilities have been disclosed in the vm2 Node.js library that could be exploited by...

On May 5, 2026, at roughly 19:30 UTC, DENIC, the registry operator for the .de country-code top-level domain (TLD)...

The Iranian state-sponsored hacking group known as MuddyWater (aka Mango Sandstorm, Seedworm, and Static Kitten) has...

Analysts recently confirmed what identity security teams have quietly feared: AI agents are being deployed faster than...

Palo Alto Networks has released an advisory warning that a critical buffer overflow vulnerability in its PAN-OS...

A security researcher has discovered that Microsoft Edge will load all your stored passwords into memory in plaintext...

When you purchase through links on our site, we may earn an affiliate commission. Google has posted its changelog for...

A newly identified supply chain attack targeting DAEMON Tools software has compromised its installers to serve a...

The activity is being tracked by Cisco Talos under the moniker UAT-8302 , with post-exploitation involving the...

While the software industry has made genuine strides over the past few decades to deliver products securely, the...

The North Korea-aligned state-sponsored hacking group known as ScarCruft has compromised a video game platform in a...

Microsoft has disclosed details of a large-scale credential theft campaign that has leveraged a combination of code of...

An active phishing campaign has been observed targeting multiple vectors since at least April 2025 with legitimate...

Every BI team knows this bottleneck: a business user has a question that falls outside existing dashboards, so they...

Security for cloud infrastructure is no longer defined by a single control, product, or boundary. Modern threats...

cPanel Flaw Comes Under Attack —A critical flaw in cPanel and WebHost Manager (WHM) has come under active exploitation...

In 2025, LLM-backed chat and agent systems crossed a threshold, going from useful but error-prone coding assistants to...

The China-based cybercrime group known as Silver Fox (aka Monarch, SwimSnake, The Great Thief of Valley, UTG-Q-1000...

A previously unknown threat actor has been observed targeting government and military entities in Southeast Asia...

Written by Adrian Kingsley-Hughes, Senior Contributing Editor Senior Contributing Editor May 3, 2026 at 5:00 p.m. PT...

Cybersecurity company Trellix has announced that it suffered a breach that enabled unauthorized access to a "portion...

A newly discovered Vietnamese-linked operation has been observed using a Google AppSheet as a "phishing relay" to...

Cybersecurity researchers are warning of two cybercrime groups that are carrying out "rapid, high-impact attacks...

Cybersecurity researchers have disclosed details of a new China-aligned espionage campaign targeting government and...

Department of Justice (DoJ) on Thursday announced the sentencing of two cybersecurity professionals to four years each...

In yet another software supply chain attack, threat actors have managed to compromise the popular Python package...

Passkeys are designed to replace passwords with strong, phishing-resistant credentials that make sign-in quick, easy...

Today marks the end of our first Agents Week, an innovation week dedicated entirely to the age of agents. It couldn’t...
![Reference image for: [Webinar] Find and Eliminate Orphaned Non-Human Identities in Your Environment](https://patricktechmedia.com/media/source?src=https%3A%2F%2Fblogger.googleusercontent.com%2Fimg%2Fb%2FR29vZ2xl%2FAVvXsEi6vJpO9kksCQDpSksNkqDFNUCbXD70dMGYqI6P9S_XPMY5d8BR8PVdrsVQP1ZJO_-nzL6eQShM3Cap9heQ5kAglsPjfxwIcXPSsf_cfgUVnGQ2XzIWVOuo7JhxMjnHYDN6r9KlQ6LqZJisRZkjatnWChuzUkSlXRa1hFseUPq28PZ5gjGR7L2WzTFdZ3fM%2Fs1600%2Fghost.jpg)
In 2024, compromised service accounts and forgotten API keys were behind 68% of cloud breaches. Unmanaged non-human...

A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination...

An Iran-nexus threat actor is suspected to be behind a password-spraying campaign targeting Microsoft 365 environments...

Hong Kong has a small but strong community, and their energy and passion are high. Last week, I visited AWS Hong Kong...

For security leaders, this creates a costly operational gap : slower validation, limited early-stage visibility, more...

Today I want to talk about meeting people’s needs — and how their fast-evolving expectations are shaping what we...

Billions of people rely on an Internet built on open source software — which is software anyone can use — but that...

And that’s a wrap on the 62nd Munich Security Conference (MSC) . As the premier forum for global security policy, this...

That’s because of quantum computers — computers capable of solving problems that even the most powerful classical...

Models Datasets Spaces Buckets new Docs Enterprise Pricing --[0--> --]--> Back to Articles Hugging Face and VirusTotal...

We want to reassure our users that Gmail’s protections are strong and effective. Several inaccurate claims surfaced...